In this tutorial I am going to show you how to create a WiFi Relay using your Raspberry Pi. This will allow your Raspberry Pi to connect to a Wifi AP and then also broadcast it’s own WiFi, and route that traffic over the original WiFi AP.

So why would you want to do this?
So you may be wondering “Why would I want to relay wifi”, well there are lots of legitimate and admittedly illegitimate reasons for doing so. My purpose for making this myself was for a work reason. Our company issues us consultants with a 4G dongle (a ZTE MF821) per client site. The ZTE MF821 has wifi capabilities built in however it only allows for 5 connections at most at any time, which really doesn’t work when you’re working on a project that has a full compliment of staff working and needing internet access. So I needed a way to relay this internet connectivity on a new AP that didn’t have the limitation of 5 devices. And that’s my Raspberry Pi.
To make it an even cooler solution, I decided to impersonate the WiFi back at our head office. And because every consultant has the company WiFi already stored in our devices, as soon as a colleague walks onto client site, they are instantly connected. Very Cool!
So let’s begin!
What you will need to do this tutorial:
-

Raspberry Pi Model B+ A Raspberry Pi (of course!)
Either the Model B or B+ is perfect for the task, but don’t overclock it, it’s unnecessary for this task. - 2x WiFi adapters that are linux compatible
I highly recommend using TP-Link WN722N, they are awesome adapters and compatible with nearly anything. However if you haven’t got one of these and need to find an adapter that will work, google “Kali WiFi Adapters” and you will find lists of highly compatible devices to buy. -

Samsung 16GB Micro SD A fresh Raspbian on a SD / Micro SD card ready to go!
I will be using the Raspbian Wheezy 2014-09-09 release during this tutorial. Make sure you have completed the Raspbian config utility prior to starting this guide.
Assumptions:
This guide will assume that:
- You have completed the Raspbian Setup Utility
- You are connected to your raspberry Pi and can create a shell session either by eth0 or a console cable. Warning! if you connect via WiFi it could affect your ability to do this tutorial successfully.
- We will be using nano as a editor in this tutorial, and putty as a shell. Vim people – don’t be haters 🙂 and mac users can use the ssh command in your terminal in lieu of having putty.
- You have a working understanding of setting up a WiFi network using a retail piece of equipment.
- You have a working understanding of basic network configuration (DHCP servers and clients, IP addressing, subnets and routing)
- You have a working understanding of the basics of linux, such as editing files, traversing the file system and using basic applications.
Okay, let’s begin!
So the first thing we will do is make sure our Pi and it’s packages are updated:
apt-get update -y
Now we need to grab all the packages we will be using for this process:
apt-get install hostapd hostap-utils iw dnsmasq -y
Once this completes it’s time to setup our hosted AP.
Part 1 – Setup the Raspberry Pi WiFi AP
Editing /etc/network/interfaces
The first thing we need to do is attach a wifi adapter to become wlan0, so go ahead and do it now. It may take up to 30 seconds for the devices to fully install and register. To see if this is completed keep running ‘iwconfig‘ until you see wlan0 appear.
Now we need to configure our new network. We will be using wlan0 for the Raspberry Pi’s WiFi AP and wlan1 later as the client of the existing WiFi AP. You can use a different IP Address range and subnet if you wish but we will be using 192.168.10.0 / 255.255.255.0 for this tutorial for our hosted AP and issued DHCP leases.
Let’s edit /etc/network/interfaces and setup the correct configuration for our adapter. We need to make sure that our wlan0 is configured with static ip addressing on the correct subnet rather than the default conf which is occasionally loaded by the OS (don’t panic if all you see is the first three lines of the screenshot, just append to the end of the file.) Start the editor by running the following command:
nano /etc/network/interfaces
Now remove the preexisting configurations in this file in reference to wlan0 and then append the following to the end of the file:
allow-hotplug wlan0 iface wlan0 inet static address 192.168.10.1 netmask 255.255.255.0
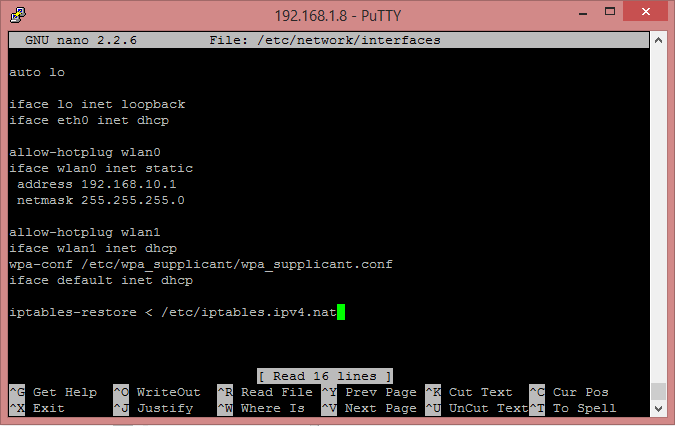
Your file should now look like this:
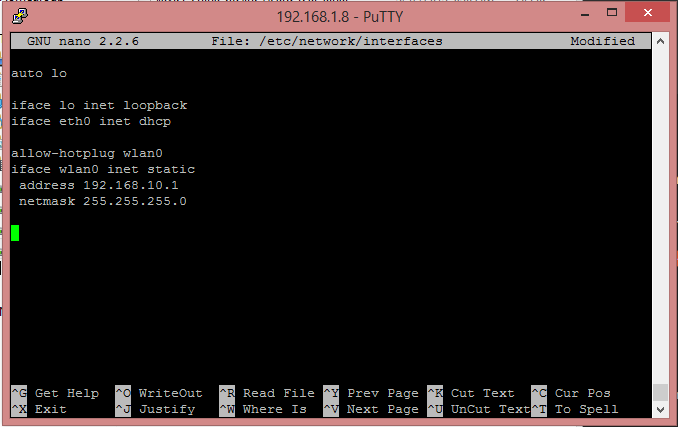
Hit Ctrl+X and press Y to save and exit nano.
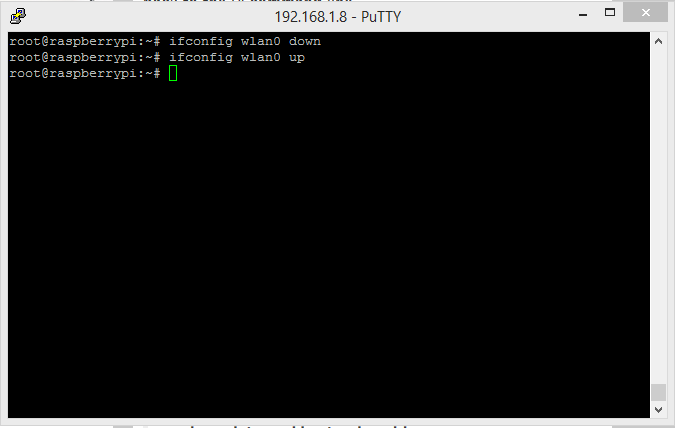
To confirm that your file is configured in a ‘sane’ way, lets bring down the adapter and put it back up again by running the following two commands:
ifconfig wlan0 down ifconfig wlan0 up
If there is an error in our configuration then you will see output when you try to put the adapter back up. However I am sure yours will look just like mine does below:
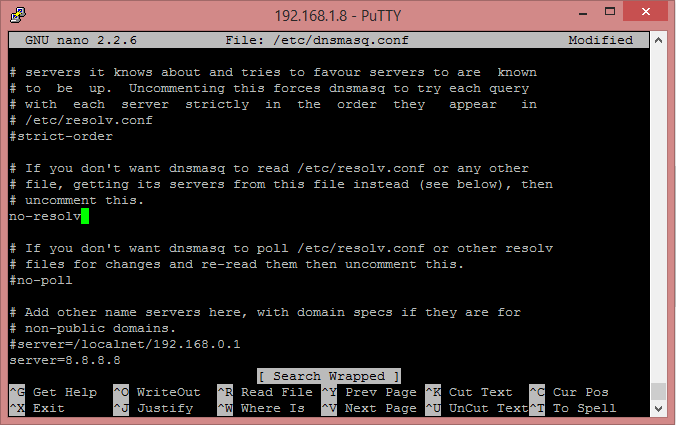
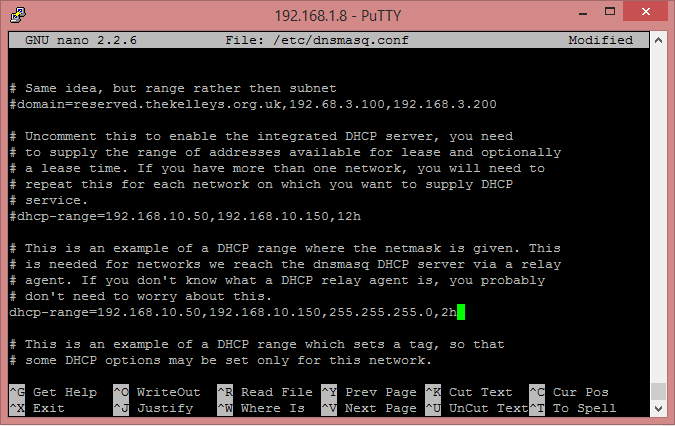
Configure DHCP – Editing /etc/dnsmasq.conf
OK now that our network adapter wlan0 is statically configured, we need to configure dnsmasq. The config file for this is HUGE! you will have to make use of the search in nano (Ctrl+W, type string to search for and hit enter. to repeat a search press Ctrl+W and then hit enter).
Edit /etc/dnsmasq.conf by running the below command:
nano /etc/dnsmasq.conf
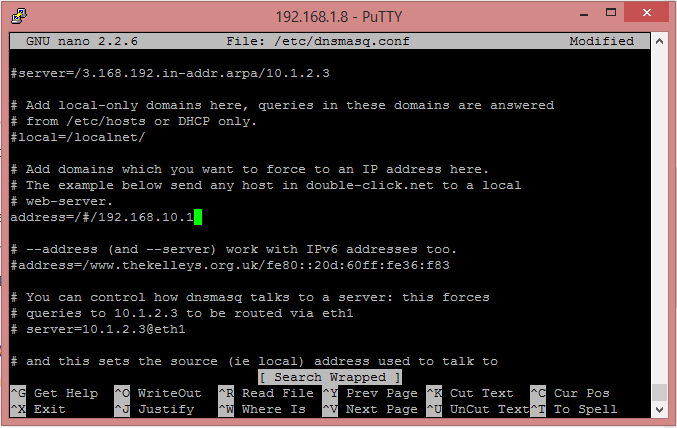
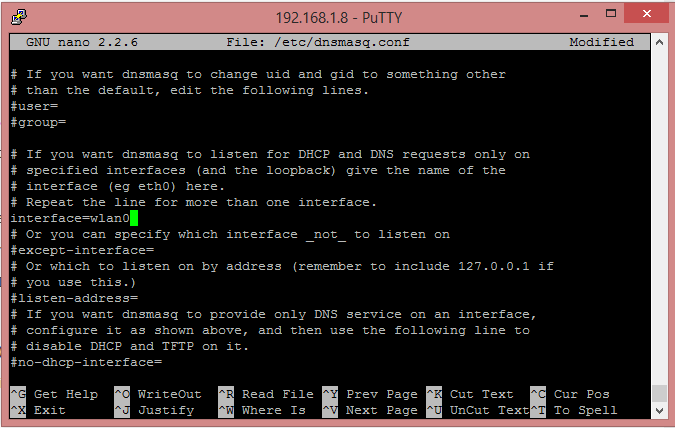
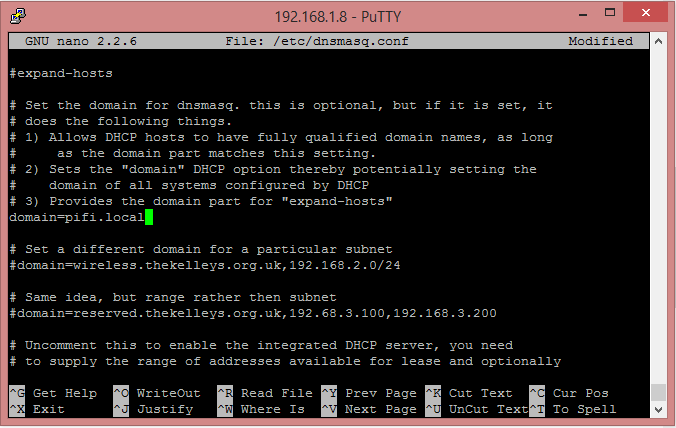
The make the following adjustments:
- Search for #no-resolv, remove the leading # to uncomment this line
- Search for #address= and change this line to be:
address=/#/192.168.10.1
- Search for #interface= and remove the leading hash to uncomment the line, and then add wlan0 after the = sign.
- Search for #domain= remove the leading hash and then change it’s value to pifi.local (or whatever else you would like).
- Search for #dhcp-range and remove the leading hash, then change the line to read:
dhcp-range=192.168.10.50,192.168.10.150,255.255.255.0,2h
Hit Ctrl+X and press Y to save and exit nano.
That’s the worst part of the configuration sorted for this tutorial. The other config files are a lot easier to deal with I promise.
Configure hostapd – /etc/hostapd/hostapd.conf
OK now we need to configure our WiFi AP that our Raspberry Pi will be broadcasting for our clients to connect to.
Edit /etc/hostapd/hostapd.conf by running the following:
nano /etc/hostapd/hostapd.conf
Erasing anything that is pre-existing in this file, paste in the below configuration whilst changing the values for ssid and wpa_passphrase to whatever you like.
interface=wlan0 driver=nl80211 ssid=PiFi hw_mode=g channel=6 macaddr_acl=0 auth_algs=1 ignore_broadcast_ssid=0 wpa=2 wpa_passphrase=MyPiFiPassword123 wpa_key_mgmt=WPA-PSK wpa_pairwise=TKIP rsn_pairwise=CCMP
Warning: You need to be extremely careful with the formatting of this file;
- Wrap values with spaces in them with quotes “”
- Ensure there is no leading or trailing white space on any line
- Make sure there is no white space between the key=value elements
- Make sure there are no blank / empty lines at the top or bottom of the file.
hostapd is very particular about what it likes to consume.
Once your config looks like the below….
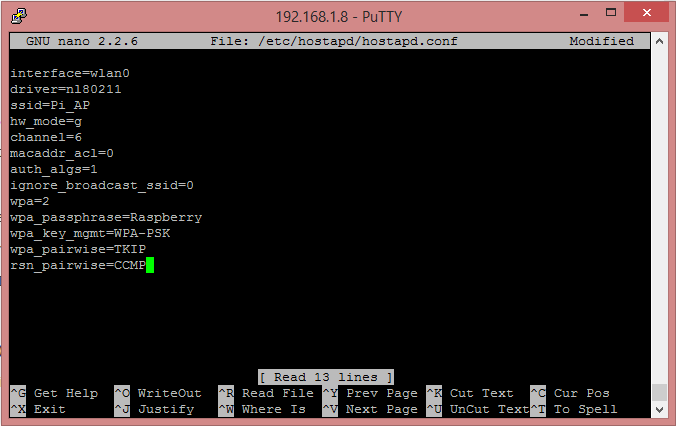
Hit Ctrl+X and press Y to save and exit nano.
Now it’s time to test out our WiFi AP!
Run the following command to start hostapd and broadcasting your new AP.
/usr/sbin/hostapd /etc/hostapd/hostapd.conf
And you should see the following…
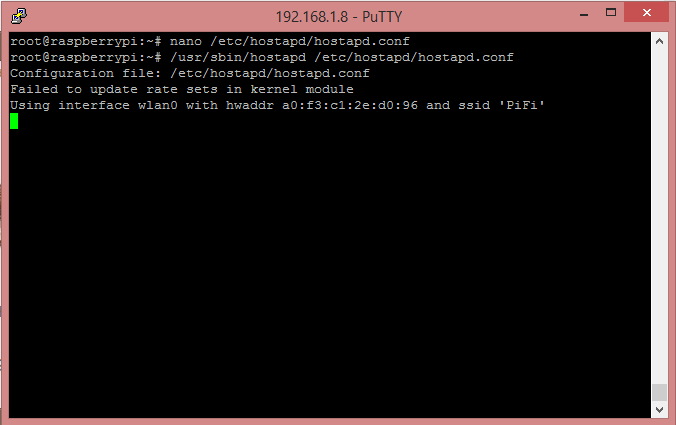
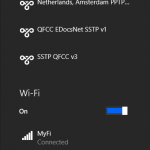
And if you check on a PC with wifi you will see your new WiFi AP being broadcasted!
If you now attempt to connect to the wireless AP using the credentials you set earlier then you should connect to the wifi, get a dchp lease and even be able to connect to your raspberry pi over it!
However for now we need to stop this wfi and continue with our configurations before we make it permanent, so go ahead and hit Ctrl+C to stop the wifi and regain control of your shell.
The last thing we will do is run a command to make sure that dnsmasq and hostapd will start at boot:
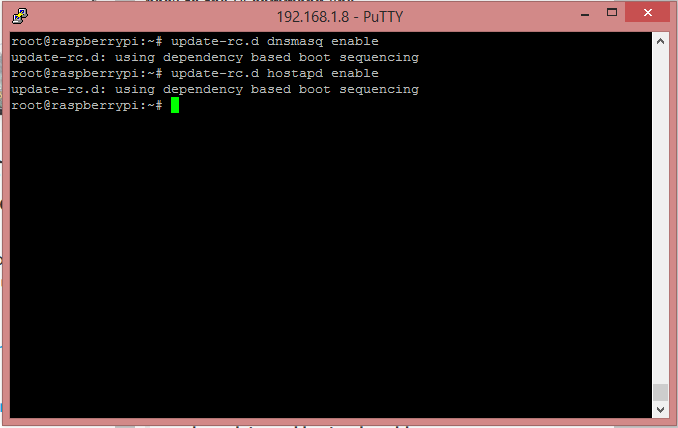
update-rc.d dnsmasq enable update-rc.d hostapd enable
And you should see the following:
Part 2 – Configure wlan1 to be a WiFi Client
Now you can connect your second WiFi adapter which will install and become wlan1, just as before you can keep running iwconfig until you see wlan1 come online.
Edit /etc/network/interfaces again
Open up /etc/network/interfaces using the following command:
nano /etc/network/interfaces
And below our settings for wlan0 with a empty line between for nice readability, enter the following configurations for wlan1
allow-hotplug wlan1 iface wlan1 inet dhcp wpa-conf /etc/wpa_supplicant/wpa_supplicant.conf iface default inet dhcp
Hit Ctrl+X and press Y to save and exit nano.
Configure wlan1’s WiFi client settings – Edit /etc/wpa_supplicant/wpa_supplicant.conf
Open up /etc/wpa_supplicant/wpa_supplicant.conf using the below command:
nano /etc/wpa_supplicant/wpa_supplicant.conf
When you open this file you will probably see couple lines already populated, if so just edit the file to look like the below, otherwise paste the configuration below into the editor, and then change the settings as needed to the WiFi point you want wlan1 to be connected to.
ctrl_interface=DIR=/var/run/wpa_supplicant GROUP=netdev
update_config=1
network={
ssid="YOURSSID"
psk="YOURPASSWORD"
# Key management type can be: WPA-PSK or WPA-EAP (Pre-Shared or Enterprise)
key_mgmt=WPA-PSK
}
Once you have updated the configuration to match the above / your personal WiFi setup hit Ctrl+X and then press Y to save and exit nano.
Now it’s time to reboot your device, when it starts up it should try to connect to the WiFi point you set in here, run the following command to restart the pi:
reboot
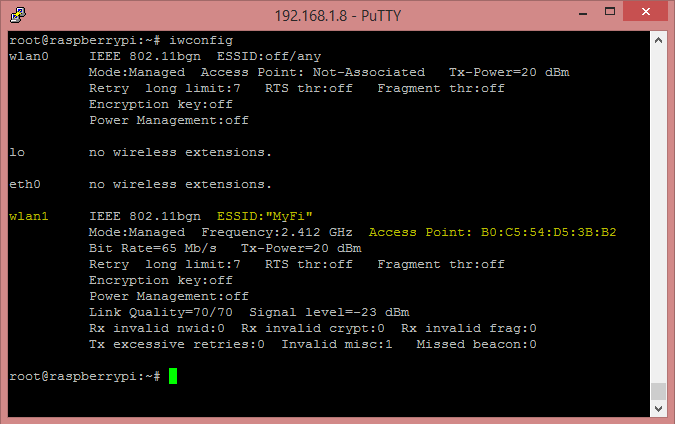
Once the pi starts up and you’re logged in again, you can confirm that the pi is connected to your WiFi on wlan1 by running the following command and looking at the data for wlan1:
iwconfig
You should see the following, just with your WiFi details:
Routing traffic between wlan0 and wlan1
OK we now have a working WiFi AP on wlan0 which issues DHCP leases and we have a working WiFi client on wlan1 which can browse the other WiFi AP’s network (and presumably the internet). So now we need to rout traffic inbound to wlan0 to wlan1 and returning traffic from wlan1 to the requester on wlan0.
We do this in just two steps.
Enable IP Forwarding – /etc/sysctrl.conf
Open /etc/sysctrl.conf by running the below command:
nano /etc/sysctrl.conf
Search for “net.ipv4.ip_forward=” then remove the leading has symbol making sure your line looks like the below:
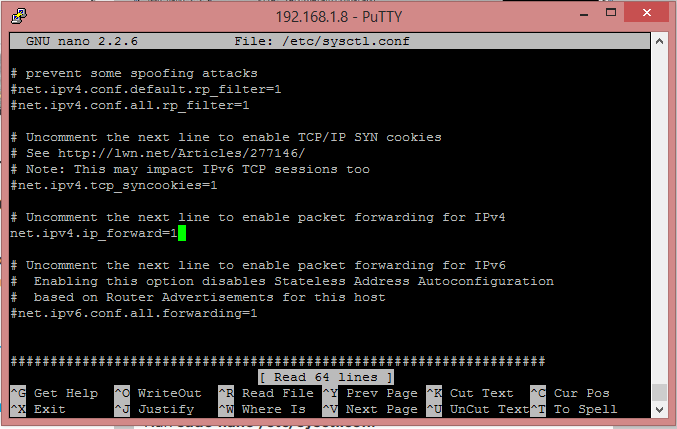
Hit Ctrl+X and press Y to save and exit nano.
And because we want to save ourselves a reboot we will hot activate it for this boot by running the following:
sh -c "echo 1 > /proc/sys/net/ipv4/ip_forward"
Enter iptables rules to route traffic between the adapters wlan0 and wlan1
This is really simple, just send the following commands in the shell:
iptables -t nat -A POSTROUTING -o wlan0 -j MASQUERADE iptables -A FORWARD -i wlan0 -o wlan1 -m state --state RELATED,ESTABLISHED -j ACCEPT iptables -A FORWARD -i wlan1 -o wlan0 -j ACCEPT
Then we will save these routes to file to be loaded again when the server boots.
sh -c "iptables-save > /etc/iptables.ipv4.nat"
Lastly we need to edit /etc/network/interfaces one last time to add a command that will load these iptables rules when the server boots.
Open /etc/network/interfaces using the below command:
nano /etc/network/interfaces
And at the very end of the file append the following:
iptables-restore < /etc/iptables.ipv4.nat
If your configuration now looks like the below….
Then press Ctrl+X and then press Y to save and exit nano.
That’s it! You’re all done!
Congratulations, you made it if you reboot your pi when it starts you should see in about 1 minute your wifi AP appear and if you connect to it, you should be routed from wlan0 to wlan1 and out to the other WiFi AP.
In my introduction I mentioned that in my real world application of this setup I am pretending to be a WiFi AP in another location. To achieve this yourself all you need to do is configure your hostapd file (/etc/hostapd.conf) to the same settings as the original AP, then when devices walk in rage of your WiFi AP it will connect to it perfectly.
Where to now?
Well you could:
- See if you can apply the above logic to create a WiFi AP for eth0.
- Create a VPN client connection on your Raspberry Pi and route wlan0 out that effectively creating a secure VPN WiFi AP.
- Test your dark side and sniff traffic going between wlan0 and wlan1 (for this use the Kali distro for Raspberry Pi as a base).
- Create a mesh of roam-able WiFi points all around your house and in your back yard.
- Write a comment below 🙂
Thanks for reading!
Xavier.